 We have confirmed reports that numerous websites hosted at GoDaddy have been hacked with myblindstudioinfoonline[dot]com malware, including WordPress blogs.
We have confirmed reports that numerous websites hosted at GoDaddy have been hacked with myblindstudioinfoonline[dot]com malware, including WordPress blogs.
Our first confirmed report of an infected site hosted at Go Daddy was on September 17, 2010 at 5:27pm, the time in which all the .php files were changed.
At this time, it is unclear as to whether any other hosting provider has been affected.
This is dangerous malware and can infect your computer!
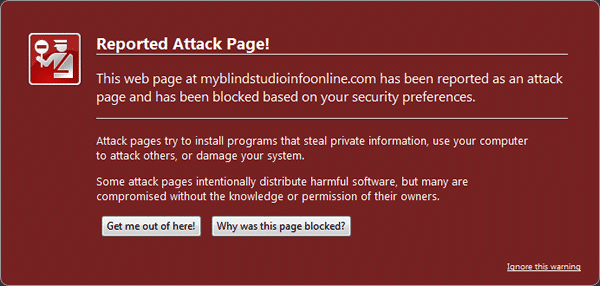
This malicious script get injected into .php files, which redirects website visitors to a fake AV page. This fake AV page attempts to make the user think they're computer is infected and offers a solution to fix it by downloading a program.
Symptoms of myblindstudioinfoonline[dot].com malware
- When visiting an infected website, it redirects you to another website with a message that says your computer is infected and tries to download a fix.WARNING: Do not attempt to visit any website links without protecting your computer first with a good, up-to-date antivirus program like AVG and MalwareBytes and a firewall.
- The .php files located on the server have the same “last modified” date and approximately the same time.
- Located at the top of each changed .php files is a very long code that may contain something like base64_decode.
- When viewing the source code from an Internet browser, the following script is found towards the bottom of the file just before the closing </body> tag:<script src=”myblindstudioinfoonline[dot]com/ll[dot]php”></script>
Blacklisted by Firefox Google
Luckily, FireFox and Google have blacklisted http://myblindstudioinfoonline[dot]com.
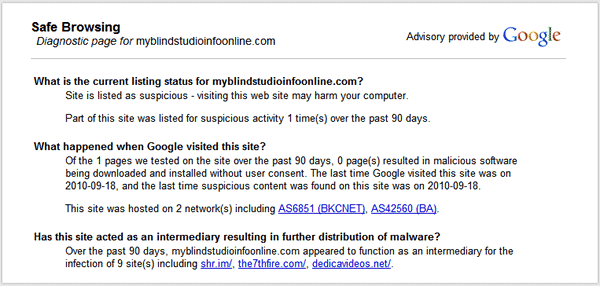
You can view Google's report here: http://safebrowsing.clients.google.com/safebrowsing/diagnostic?site=www.myblindstudioinfoonline.com
According to Google's Safe Browsing report, this website has not resulted in malicious software being downloaded or installed without a user's consent.
Even though Google's report shows that no malicious software has been unwillingly downloaded, I am not convinced that is true. An unprotected computer can get infected by downloading this malicious software.
What else we know so far
According to Sucuri.net, other domains being used in this attack are:
- http://www3. security-power31 .co.cc (spaces in url left intentionally)
- http://www4 .megaav-soft74. co.cc (spaces in url left intentionally)
And this domain is registered to Hillary Kneber, which is the registrar from the previous attacks made on many major hosting companies in May, 2010.
How to fix your hacked WordPress website:
- Remain calm! It can be fixed!
- Run a virus scan on your computer to make sure it is not infected.
- Remove your website from the server and restore it with a clean copy.
If you're unsure how to do this, we're here to help you! Contact us.
If you'd like us to fix your website for you, see our WordPress Hacking, Virus, and Malware Removal and Website Restoration package.
How to monitor your website for malware
Monitoring your website for malicious activity is essential for any webmaster. If your site gets hacked and goes undetected you risk infecting your visitors' computers and your reputation.
You can put your website on autopilot for malware scans with Web Integrity Monitoring by Sucuri. It detects any unauthorized changes to your website, DNS, whois or SSL certificates. They scan your website (even hourly) for malware, viruses, spam and security issues.
We highly recommend this service and use it ourselves. No webmaster should be without it! Use our discounted affiliate link below and save.
Go to: https://wpsecuritylock.com/sucuri (Only $7.99/month or $79.99/year)
Update:
We will update this section as new information comes it.
09-18-2010 at 11:31 am CST – We contacted GoDaddy and they are aware of this situation. They are currently working on it and will give us an update soon.
09-18-2010 at 2:43pm CST – Go Daddy released this statement to us to share with you.
An exploit affected PHP files on approximately 150 Go Daddy accounts Friday afternoon. Go Daddy's Security Team worked quickly to clean and restore these websites, however, we have detected additional customer sites that may currently be experiencing difficulties due to this same attack.
Go Daddy's Security Team has identified the cause. Our forensics have determined malicious files are being uploaded via FTP to customer websites. Go Daddy is asking all customers who believe they have a problem to change their FTP passwords.
Meantime, our team is working swiftly to restore all affected websites and appreciates customer feedback. Go Daddy will continue to monitor as long as it takes to ensure our customer accounts are clean.
If you suspect your site was impacted, please fill out our security submission form, located here – http://www.godaddy.com/securityissue.
Thank you,
Todd Redfoot
Go Daddy Chief Information Security Officer
09-20-2010 at 10 am CST – I just posted a new statement from Go Daddy and more information about the myblindstudioinfoonline malware and some WordPress security tips – read it here.
We need your help
If your website's been infected and you're not hosting at GoDaddy, let us know. If you find any new domain redirects being used in this attack, share it with others. Let's work together as a community to protect each other. Share your comments below.
Securely yours,
Regina Smola
WordPress Security Specialist
Follow @WPSecurityLock
Become a Facebook Fan
P.S. Help spread awareness by telling others, share this article on Twitter and Facebook.

Hi, I have http://somosemprendedores.com/ attack on my blog
This appears in the source code at the bottom of the page:
Please help urgently. I stay at alocte.net, a reseller of Go Daddy
Hi, I have somosemprendedores [dot] com attack on my blog
This appears in the source code at the bottom of the page:
=”http:// myblindstudioinfoonline [dot] com [dot] ll [dot] php”
Please help urgently. I stay at alocte[dot]net, a reseller of Go Daddy
Hi Genner,
Thanks for your comment. Remain calm! It’s going to be okay.
Can you please email me directly so I can help you?
https://wpsecuritylock.com/contact/
I am posting an announcement about this now and will get back to you shortly.
Yesterday three of my sites (hosted by GoDaddy) were hacked again.
Sorry to here you got hacked again. Did you get them fixed? And what did Godaddy say?
My site was part of the attack yesterday, and it threw me into a panic. I changed all my passwords right away and tried to isolate the damage at least. When I did submit a ticket to GoDaddy, it took them all of 15 minutes to get back to me saying they had cleaned my files of the code. So in that regard, I am very grateful. I’m not sure if it makes me feel better or worse to know that others were dealing with this same issue and it had been put on GoDaddy’s radar.
By the way, in all the reading I’ve done about malware in the past 24 hours, I’m glad I found your site. Definitely going to check out all the options for protection!
Stacey,
Happy to hear you got the help you needed fast, it’s been a busy couple of days for Godaddy I’m sure. I congratulate you on your clear thinking and quick action it may be just what saved your website from an even worse fate.
Stop on the site soon and catch up on the articles full of tips and strategies for protecting your site and messing up these evil hackers.
Thanks for your comments, Regina
Regina I am so glad I met you before any of this happened to me! I have implemented most of what you recommend, still working on the last few pieces!
Thanks so much for creating this site and letting people know there is a light at the end of the tunnel.
You do GREAT work and provide even GREATER service.
tks
Carla
Thanks Carla,
Regina will be so glad to hear she could be of service. Please let me know if there is any way WPSecurityLock can help if a crisis should arise. Prevention is key when is comes to hackers. Glad to hear you’re safe!
Make It A Great Day,Paula
Regina – Thank you for this post –
I am not clear –
Are these only Godaddy hosted WordPress sites that have been hacked or are some of GoDaddy’s other template files vulnerable?
I have a client hosting their account on Godaddy using their WYSIWYG templates.
Terry
Terry,
Thanks for your comment.
I am unclear as to whether or not it is just WordPress sites hosted at GoDaddy. My guess is that hackers are targeting any .php file of accounts they can break in to. You should check to see if .php files all have the same date and approx. time for yesterday or today.
Regina
Good on ya for the quick alert! Nicely done, and thank you for being there! I don’t have any sites on GoDaddy anymore, but if I did I’d be really thankful for you doing this if I had.
That’s really cool of you Regina, cheers!
Wayne
Thanks Wayne,
How nice of you to say! Remember to spread the word about security threats and other hacker destruction. It is such a crime that these vicious people can step in and do so much damage to someones hard work and dreams.
Prevention and vigilance can go a long way to protecting peoples sites and lively hoods.
thanks for the info.. i was shocked to see the attack…
used this fix steps and things were working again…
http://alltips.in/how-to-fix-godaddy-malware-attack.html
thanks again.
My site hosted by GoDaddy was affected yesterday, 9/17/10. What really infuriated me is that I contacted GoDaddy 3 times this morning and was told that they knew of no problems which I now find was not true. They knew last night that there was an issue.
I think my site is fixed now but I’m seriously thinking of getting off of GoDaddy completely.
To: BLKCATGAL
Wow, it sounds like you had a real time of it! We hope everything is going well now. Thank you for sharing your experiences and helping to spread the word.
Sigh. This is the second time in about 6 months that my godaddy hosted WordPress account has been hacked. I sent a ticket to the security link above and I’m waiting on GoDaddy to respond. I’m hoping they clean up all the files so I don’t have to. Again.
Infuriating. What’s weird is that I know its been hacked as the WP admin panels are hosed up. But neither Kapersky nor Firefox showed the infection. I received an email from a regular reader.
Appreciate the updates.
K
Hi Kristy,
Thanks for your comment.
Sorry to hear you got hacked again. Did you get it fixed? GoDaddy released a statement that they fixed all affected websites. You can read it here: https://wpsecuritylock.com/godaddy-resolves-myblindstudioinfoonline-malware-hacked-websites/
Regarding Kapersky and other programs notifying you about threats, when a new malware or virus is discovered it takes them time to update their threat definitions. Be sure that you have a good firewall on your computer too. For more help with PC safety, be sure to get Allen Dresser’s free report at http://internettecguy.com
You can also have your site on 24/7 monitor with https://wpsecuritylock.com/sucuri (our affiliate link which gives our readers a discount).
Stay safe!
Regina
Thanks, Regina, for getting the word out so quickly. You’re the greatest! I use the file monitor plugin on my wp sites and so far it’s done a great job of alerting me whenever a file has been modified ( eventhough 99% of the time, it’s just an update). Between that plugin and the anti-malware one, I’ve managed to stay on top, and was alerted instantly when I did get hacked.
keep up the good work and
continue Slapping them hackers ^.^
Kathy Pop
Go Daddy submitted a new statement that they’ve cleaned and restored all affected websites. I posted this statement along with some WordPress security tips here – https://wpsecuritylock.com/godaddy-resolves-myblindstudioinfoonline-malware-hacked-websites/
I was attacked on Friday around 3:36 pm PST. I was online working on my site when I received a message from my Norton Internet Security software informing me that my computer was saved from an attack (http://www3 .security-power31 .co .cc). I then checked out my site on Go Daddy the next day and discovered all of the changed scripts (I definitely knew something was amiss because my WP dashboard looked horribly wrong, but my website looked fine). I contacted Go Daddy immediately on Sunday, received an answer from them as to how to remedy the problem (which thankfully they did for me), but they neglected to tell me about the attack. I knew, however, that if this was an attack (which I suspected all along) you guys would clue me in – thanks a bunch!
Peace,
Michelle 😉
Sorry to hear your site was attacked, but I’m glad you got it fixed! It’s such a pain when sites get hacked. I wish these malicious hackers would find something useful to do.
Make sure you change your FTP password if you didn’t already.
Also, change your database password and secret keys too. According to Go Daddy, it was an attack via FTP and that means hackers could access your wp-config.php file which contains that information.
If you’re ever attacked and you get it fixed, make sure you clean your browsers cookies and clear your cache so you’re admin looks normal again.
Thanks for your comment and let us know if you need any help.
~ Regina