The team here at WP Security Lock have received numerous inquiries from victims that have compromised sites. As we began to dig in, we started to see one common theme between them all “OptimizePress 1.x.”
Some of the clients had the latest OptimizePress version (1.6.1) and others had an previously version of 1.x which were hacked.
Upon further review, we found that OptimizePress released an article called “Important OptimizePress 1.0 Security Update” on their website.
This is an important announcement for OptimizePress 1.0 users. (Please note this does NOT apply to OptimizePress 2.0 which is built with a completely new codebase)
Back in April 2013 we discovered a potential security flaw in part of the code for OptimizePress 1.0. Our developers quickly patched this issue and we released an update to the platform. We also announced this to our customers via email, although it appears now that many of our users may not have received this email.
They stated that they updated the following files to fix the security vulnerability in OptimizePress version 1.6.1:
- OptimizePress/lib/admin/media-upload-lncthumb.php – updated April 12, 2013
- OptimizePress/lib/admin/media-upload.php – updated April 12, 2013
- OptimizePress/lib/admin/media-upload-sq_button.php – updated April 12, 2013
Their solution was that if you had an OptimizePress version previous to 1.6.1, you need to deactivate the theme, delete the files, and then install version 1.6.1. Then run a security scan on your site. << READ UPDATE BELOW
We agree with this solution and don't forget to make a complete backup first. However… that doesn't remove a vulnerable file that we still see exists in their current theme.
We found that there is an vulnerable jquery file in the theme itself. This file is not called by theme directly, but it still poses a security risk leaving it on the server. We also found a couple other outdated script, but did not see any current security issues with them.
For added security we request that you not only update your OptimizePress version 1.x to 1.6.1, but also delete the following file:
wp-content/themes/OptimizePress/js/jquery-1.3.2.min.js < XSS injection vulnerability
Also, if you have any “test” or “development” sites that you aren't using or forgot about be sure to update them as well and remove that file. Do a little housekeeping and do a quick review of your sites and remove any you no longer are using.
After further investigation, it was amazing how many sites are indexed by search engines using this file. Scary for those webmaster and useful for the bad guys.
Here is what else took place today when we contacted OptimizePress support.
While reading their article, we saw the following statement:
If you don't know how to update your site – please send us your WordPress administrator logins, your site URL (address) and your FTP or Cpanel details if you know them and we will update your site
That sounds very helpful doesn't it? I think it's great they want to help their paying customers update their site's theme.
However, at the bottom of the article, you click to Submit a Ticket.
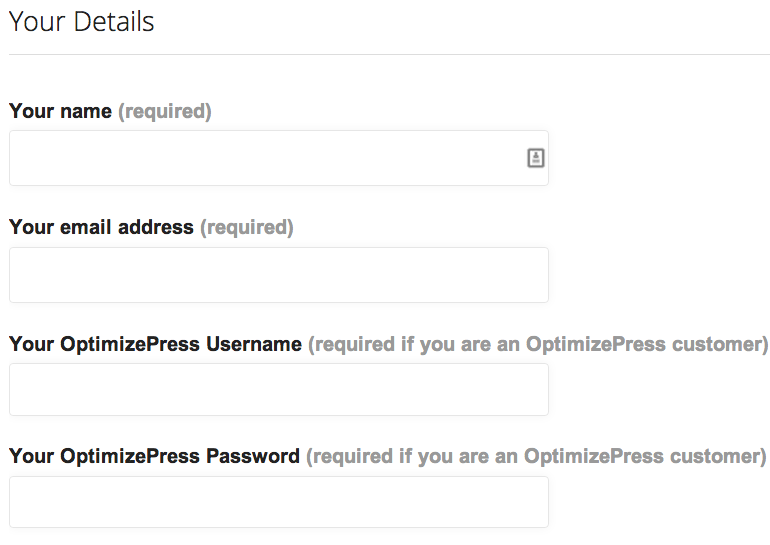
Wait. Hold your horses!! Bells and whistles sounding. The site is not on an SSL certificate and I'm supposed to put in my OP username and password?
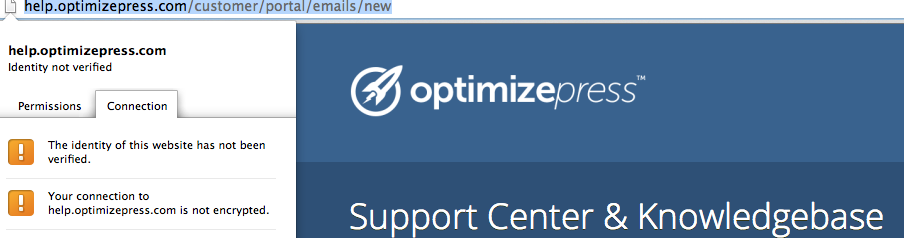
Remember earlier when it said OptimizePress would help you update your theme and they wanted you to send them your “WordPress administrator logins, your site URL (address) and your FTP or Cpanel details?” Please don't do that on any non-secured form (including theirs) and always use caution when you give out this information. It's the keys to your site kingdom. It gets sent over plain text and there is no secured connection. Plus you don't know where that information is being sent to or stored.
We did fill out their contact form (without any pertinent data) and asked what they planned to do about the distribution of the vulnerable file to their customers. We also asked that they address their insecure form and collection of usernames and passwords for your safety.
OptimizePress has been around along time and I am sure they care about their customers. We are hoping that they move quickly to resolve these issues.
UPDATE 12/12/2013 at 6:30pm CST:
Cindy Bidar logged in to OptimizePress and found that version 1.6.2 was just released and has removed the vulnerable file.
Here's what you need to do:
- Download OptimizePress 1.6.2 (Again, this does not affect OP 2.x users)
- Login to your WordPress Dashboard
- Appearance > Themes > activate another theme such as Twenty Twelve
- Delete OptimizePress 1.6.1 or an earlier version.
- Install OptimizePress 1.6.3
- Activate OptimizePress 1.6.3
- Run a malware scan on your site
UPDATE 12/13/2013 at 1:15pm CST:
Regina Smola received a response from OptimizePress as follow:
Hi Regina
We have had our developers look into this and they advised they did not think this file was a security risk – however for the purposes of security and peace of mind they have checked and advised that it is not required for the operation of OptimizePress, so we have removed this and updated the file in the OptimizePress 1 members area to 1.62 which includes this fix
~Laura
Regina replied with the following:
Hi Laura,Thank you for your response.What about the issue with your support ticket form collecting usernames and passwords on a non-ssl?I included that in my ticket, but you didn't answer that issue.
~ Regina Smola
In conclusion
Our job is to help educate people in staying safe online and help you protect your WordPress sites.
If you need help upgrading your OptimizePress theme, please let us know. Don't send us any login information when contacting us. Just let us know what you need help with. If any login info is needed, we will show you the secure way to send it to us.
Also, if your site has been compromised and you want us to clean it for you, you can signup for our WordPress Malware Removal Service.
Leave Your Feedback
Are you using OptimizePress version 1.x? Has your site been hacked while you were using this theme? Did you receive the notice when the security patch was released in early this year? Let's all help each other stay safe by sharing your comment below.

Leave a Reply