 Reports of WordPress blogs self-hosted at GoDaddy.com and have been infected with the losotrana[dot]com/js.php on Monday, May 17, 2010 and Thursday, May 20, 2010.
Reports of WordPress blogs self-hosted at GoDaddy.com and have been infected with the losotrana[dot]com/js.php on Monday, May 17, 2010 and Thursday, May 20, 2010.
Warning: This is dangerous malware! This scareware injection tries to infect your site visitor's computer. If your visitors do not have an up-to-date anti-virus program running, their computers could get infected.
What You Should Do: If you have an up-to-date version of an anti-virus program running, such as *AVG, please check your website now to see if it redirects you! Note: If you receive a pop-up message to download anything, do NOT click “yes” or “okay.”
If you do not have an updated anti-virus program running, do not go to your website to check. Instead, log in to your site via FTP and look at the “Last Modified” column and see if your .php files all have the same date/time (either 5/16, 5/17 or 5/20/2010).
If your website is infected, put it in maintenance mode immediately so that you do not infect your visitors. Click here for instructions on how to put your site in maintenance mode – see Step 2)
Then clean your website completely and upload a fresh copy. Be sure to check for any suspicious .php files that you did not put on your website. There must be a “trigger” file that sets this infection off. Be sure to remove it!
Losotrana Symptoms:
- Viewing your site's source code, you will see the following script injected on your pages:<script src=”http:// losotrana[dot]com/js.php”></script>
- Your site redirects you to a fake website that executes the threat that tries to download to visitors computers.
- A long string of base64_decode script is found at the top of all .php files.
- This threat has the same IP address as the holasionweb.com injection (188.165.200.96).
- Losotrana[dot]com has the same registrant as the other latest attacks and it shows that they have 203 other domains registered too. You can view the whois here, and I have copied it below for you as well.
HardSoft, Inc.
Hilary Kneber [email protected]
7569468 fax: 7569468
29/2 Sun street. Montey 29
Virginia NA 3947
us
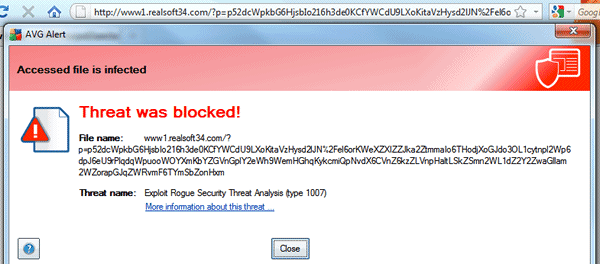
Here's a screen shot of the threat stopped by AVG on May 17, 2010
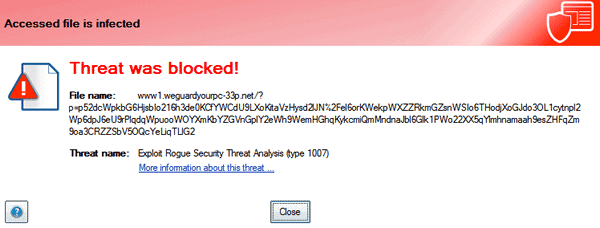
Here's a screen shot of the threat stopped by AVG on May 20, 2010
We will continue to provide information as it becomes available. on this post. WPSecurityLock has contacted Go Daddy to report this latest attack. And we are now emailing MediaTemple as well.
UPDATE 5/17/2010 at 9:20am: We're receiving reports from webmasters hosting at MediaTemple that their computers were infected and a virus has stolen their FTP passwords. Please make sure your computers are clean and that you change your FTP passwords immediately.
UPDATE 5/17/2010 at 9:58am: After further investigation, we now know that the sites hacked at MediaTemple are not related to this latest attack. They are an isolated incident and not related to the losotrana[dot].com/js.php script.
So far, the only verified reports of websites attacked with this issue are hosted at GoDaddy only.
UPDATE 5/17/2010 at 10am: We have received correspondence from Go Daddy's Information Security Operations team. They are aware and working on this issue. They will be providing a statement very soon to give you an update.
UPDATE 5/20/2010 at 10am: We are receiving multiple reports that the lostrana[dot]com/js.php script is rearing its ugly head again today! Please keep an eye on your websites. Some are redirecting to http://webguardyourpc-33p[dot]net/…. (see screen shot above)
UPDATE 5/20/2010 at 5:15pm: Go Daddy is reaching out to our community and has provided the latest statment regarding today's attacks:
Compromised Website Update 5/20/10
An attack impacting less than 200 accounts happened this morning.
Go Daddy is working with other top hosting providers and security experts to gather information to stop to the criminals initiating these exploits.
We have contacted the malware site registrar to remove the offending domain from the Internet, in order to block the attack.
As part of our investigation, Go Daddy has launched a fact-finding tool to collect information about your experience. If you suspect your site was impacted, please fill out our security submission form, located here – http://www.godaddy.com/securityissue.
Thank you,
Todd Redfoot, Chief Information Security Officer
GoDaddy.com
We need your help….
This new losotrana[dot]com/js.php malware was just discovered this morning (May 17, 2010) thanks to reports from our community. Please help spread awareness and come together as a community. Be sure to Tweet this message and also add it to your Facebook. If you have any new information, please leave a comment below so we can all help each other.
Securely yours,
Regina Smola
Follow me on Twitter
Follow WPSecurityLock on Twitter
* Denotes our Affiliate Link. If you a make a purchase through this link, we receive a commission.

4th time getting hacked! Every single time these attacks happen my site gets hit. Nothing better than waking up, looking at my website and getting redirected to malware. My google serps have already dropped majorly… 3 years of work going down the drain. Godaddy wont even call me or send an email, I have heard nothing. When I called their tech support line it was almost laughable. The first guy had no idea what hackings I was even talking about; the second guy blamed wordpress. This is a nightmare.
Oh yeah…woke up to the same thing! Also found several odd files buried in a few folders that would not allow me to delete them through my FPT client. They all start with “.pureftpd” then a string of numbers and letters. I was finally able to delete them through the godaddy “my files” tab in the hosting dashboard. Sent a message to godaddy via the security issues link provided by WPSL (thanks!).
The first level support people seem to have no idea that this is even happening. They just give out the standard line about WP not being their problem and say bye. If you call, demand to speak to the special security team, or to be escalated immediately. The last attack (last Wednesday) left these suspect files on my server and I was unable to even access the “my files” tab so I had to put in a help ticket to get them removed….48 hours later.
Thanks to Regina and the WPSL team for trying so hard to help!
Interesting, if I would be on GoDaddy – I would have moved after second hack. They seem to have a notorious issue they need to investigate. So many hacks in relatively short period would indicate compromised servers and their users shouldn’t have to suffer through it.
Exactly. I was one of the ones who moved after the second attack, and once again my sites are fine.
It looks like GoDaddy, by the wording of their last public statement, has finally started to look within themselves to find the source. However, it’s too little too late. If the back door hadn’t been open, these attacks wouldn’t have happened.
I’m actually surprised this has occurred for a fourth time, and it tells me my choice to move hosts was the best decision.
I feel for those of you cleaning up your sites today. You should be working on your business, not dealing with this issue again.
As for mentioning who I moved to, I have withheld that information as I do not want to look like a spammer trying to stir the pot. I am a former GoDaddy customer who got screwed just like you.
Look back at the posts WPSecurityLock has made about these attacks. There are mentions of excellent hosts in the comments section.
Do your research and make sure you are moving a clean set of files to your new host.
Good luck.
Rick,
Where did you move your sites if it’s not a secret?
I’m ready for the change.
To Where do you move?
They got my sites again too … fourth time. This is despite doing everything that GoDaddy says will supposedly eliminate risk. My sites were up to date and had been scanned by GoDaddy.
The good news is that the wordpress-fix.php fix seems to remove the code. I ran it and the code appears to be gone. I’m still hunting around for code, but it seems to be clean. It sure beats doing a full restore of multiple sites.
GoDaddy will be getting an email from me … again. The only thing I can think to do at this point is to close down that hosting account and open a new one, which of course will mean migrating four sites.
This may not be the best place to ask this, but can anyone recommend a secure web host? I’ve got seven or eight sites to move from their current home on GoDaddy.
Hi my fellow sufferers,
I have been hacked for the fourth time now. I have on Go Daddy Shared Linus hosting and even after following practically every single protective measure, this just won’t give. I am a Go Daddy customer for years and even though they are not the BEST in the world, I was under the impression that they are decent service providers. Until one fine day these hacks came into view and I contacted their Tech support. The first time around, they blamed WordPress, weak passwords and my carelessness for the hack. I honestly thought they were right. I asked them for a solution and they told me to submit a ticket and hung up.
At that time I stumbled upon this blog and read and followed the steps and my blog was fixed. I thought it was a dream but it was true. I promised I won’t be so careless ever again and followed all security measures and even thanked Go Daddy along with this blog for pointing them out.
…Then it happened again, i had updated my wp to the latest, locked down all access totally and yet it happened again. I came to this blog, followed the steps and it was fixed again. I called Go Daddy and they gave me the same crap, I told them how wrong they were and they refused to acknowledge that it was a open door at their end. I calmed my nerves, thought how good Go Daddy was till this happened and moved on.
But it happened again and again and I fixed my blog by reading this lifesaver and contacted Go Daddy, no they did not give me the earlier crap and told me this was something which might be a cause of several reasons which they don’t think necessary to tell me yet. And they said they are trying to solve this. And linked me to some crappy guides with loads of misinformation.
I have now REALIZED, how crappy and hypocritical these Go Daddy people are and how they care for their paying customers. I know we are a small number, I know we are only 1% of their users, I know this and i DO KNOW THAT. But the thing is, we paid money to them, we trusted them and we have given them work and yet they ignore us as they are very successful now.
I am moving to host other than Go Daddy, and before I leave, I am going to tell you something. Yes, the numbers are less now but it’s only a matter of time before all webmasters suffering this nightmare, take their babies elsewhere and you keep getting screwed and losing paying customers, and then I will see how insignificant and minor problem this is. You keep getting hacked by some random loser and instead of accepting your fault and apologizing to your customers, you give lame excuses and keep them in the dark. After 15 months with you, I just want to tell you one thing after talking with your customer support people even in such a crisis. Go Daddy.
**** YOU, We were your customers and you JUST DON’T CARE< JUST DONT! :'(
That’s pretty much how I feel. I’ve been hacked 5 times in the last 3-4 weeks, and while the first time was most likely my fault, I then found this blog and read up on WP security and tightened all settings, together with installing the security plugins recommended on this very blog, plus a few others. I was hacked again.
Then GoDaddy called me and I spoke to a representative who told me I needed to install the latest WP from scratch. I did that, reinstalled all my plugins, made sure permissions were tight, and sighed with relief.
How optimistic of me: I’ve been hacked 3 times since.
I’m pretty much ready to move on to another host. I registered my first domain in 1999 on GoDaddy, so it seemed natural that when I wanted to have a site go live I do it on GoDaddy too, then barely 2 months into it I start getting hacked. My site barely covers its own costs and I maintain it for fun and in my own free time. Nobody pays me to spend hours dealing with the stress of hacking, so I’m looking around for a new host. I’d appreciate recommendations.
I just spoke on the phone with a GoDaddy representative. They actually called me within 15 minutes of me sending a note to their support email address. I’ll give them credit for that, but unfortunately I’ve about run out of good will.
Anyhow…
I explained to the support guy that I’ve done everything that was suggested to secure my sites. My 99% sure all of my WP installations were up to date at the time of the first attack (can’t recall for sure because I did a site reinstall on one of them before I knew how to fix the issue without doing that) but I’m 100% certain they were up to date at the time of the second, third, and fourth times my sites were hacked. He said the security hole for the first attacks WAS related to older versions of WordPress, but for the subsequent attacks the hackers have found other ways in.
Take that for what it’s worth.
I don’t know if this is related, but my GoDaddy-hosted WordPress was also flagged by Firefox/Google. Don’t share the above symptoms, though.
Code was injected into a .js file of the theme I was using. It was an iframe:
if (document.cookie.search(“cqy=6″) == -1) {document.write(”
“); document.cookie = “cqy=6;expires=Sun,
01-Dec-2011 08:00:00 GMT;path=/”;}
In another WordPress installation, I found a errant file named “middle.php” in the default theme folder. It’s some kind of webshell. I wiped my WordPress installations, but I kept a sample of this file.
I called GoDaddy, but they blamed it on WordPress and said they couldn’t do much for a user-installation…
Godaddy is the worst hosting there is and they always get hacked.
How you can put a site on there that you need to run a business is beyond me.
You pay for cheap hosting, you get cheap hosting.
Hello Regina, I saw yesterday via FTP all my files. Php were modified, but was checking my blog and see nothing there is no attack apparently without a clutch if I hacked the three previous times. Could you do me the favor of my blog and see if anything abnormal. I contract hosting on a reseller Goaddy Alocate.net
Hello Genner,
I just did a quick scan on your site and I don’t see anything unusual. The malware scanner is showing your site as clean. Can you go to your File Manager > History and look at what you had the day before they were changed and view a php? Compare them with what’s on the server now to see what changed. Your site should not be modified unless Alocate cleaned something for you, but they would/should tell you.
That is why hostgator is better, they have security measures and a helpful staff. you can also set up a plugin called automatic wp back up and it will send back ups to your email address and then if you do get hit, you don’t lose everything.
Sorry to hear you got hacked. What time did it happen? Share with us details on what you saw. And be sure to report to http://community.godaddy.com/support.
The losostrana virus has reared its ugly head again! We have confirmed reports of multiple sites infected with it again today. Please check your websites now.
Today, my wordpress file monitor detect another file put in my hosting account in Godaddy by the hacker:
This email is to alert you of the following changes to the file system of your website
Timestamp: Thu, 20 May 2010 16:12:33 +0200
Added:
guilbert_being.php
Problem is not resolved in Godaddy…
Hi Ivan,
Wow! I’m glad you file monitor let you know. That mystery php file is the trigger. Make sure you delete it right away and look for any others. Did you report to http://community.godaddy.com/support
Yes, I reported to Godaddy. This is the response:
“Dear Sir/Madam,
Thank you for contacting the Hosting Security Team.
I ran the security scan on your web and verified that there is no malware present on your site.
A number of websites running PHP applications, such as WordPress and Joomla, have been affected by malware. These attacks have affected many hosting providers, including Go Daddy. They are a serious threat and we’re committed to eliminating them.
While transparency is something we value, when Internet users release information about the attacks, such as the code used to create them, it really only helps the hackers. As they gain clues into our investigation, it gives the attackers more power.
The origin and characteristics of these attacks continue to change from day to day. Thanks to the efforts of our team, we’ve kept the number of affected sites to a minimum (fewer than a tenth of 1 percent of the sites we host). This means we can devote a lot of attention to the compromised websites.
Your protection is our top priority. Our team of security experts is working around the clock to monitor our systems, investigate incidents and implement counter-measures to neutralize potential threats. You can find information about who is affected, what the attack is, and ways you can fix the problem here: http://community.godaddy.com/godaddy/whats-up-with-go-daddy-wordpress-php-exploits-and-malware/
Go Daddy appreciates your concern on this critical issue. We’re here to help, and are making every effort to answer your questions and concerns.
Our goal is to help you keep your website safe and secure.”
The same that in other opportunities….
Ivan, fill out my contact form and send me your URL. I’d be happy to run a scan on it.
They tried to hit me again today:
This email is to alert you of the following changes to the file system of your website at [link removed].
Timestamp: Thu, 20 May 2010 13:37:19 +0000
Added:
janella_georgianna.php
The code was removed right away. They hit the other night in the middle of the night, so I couldn’t do anything about it until morning. Then the next night they hit again, but there was no malware showing up on the site. I cleaned that up. Now this today. I too did everything GoDaddy said to do. This is happening so much I’ve lost count. I’m thinking today would have been the sixth or seventh hack.
If you have a copy of that bad file (php) please send it to me. I want to analyze it.
Sorry, I don’t. It was removed with using the wordpress-fix link.
Here we go again!
Did you get hacked today?
network solutions, godaddy, i really don’t understand why people still host at these companies?!
some commenters are experiencing their 4th attack! You are joking right? Are you also so forgiving in other aspects of your business/life?
Moving WordPress sites really is not all that hard! Actually it’s a piece of cake and it becomes a lot easier and faster once you have done it a couple of times. Worst case scenario you hire someone to do it for you.
There are so many great hosting companies around who actually use (part of the) money they earn from you to protect their environment from ugly attacks as this!
Interesting. It seems that Go daddy this time cleaned it or protected my site. Wll, I have been working on my site and had no attacks. Suddenly, I got an email from wpsecurity and right after that I got a Go Daddy email from SafeGuard. They said I had a malware injection and that they have removed it.
So it seems that they protected me right away which is at least some good news in this hideous mess. Anyway, I still ran the sucure wordpress-fix.php just in case.
Go Daddy has just released a Compromised Website Update of 5/20/10. See update in post above of 5/20/2010 at 5:15pm.
I dont have a website. It seems though every time I change pages with my browser I get a message from avast 3 times saying losotrana was blocked. How the hell is it trying to get in? and how can I stop it? It just happened again as well. Avast blocks the attack. Yet every site I visit seems to be infected!
Hi Carlin,
Make sure you keep your Avast up-to-date always and also try using malwarebytes.com too. I have both running. Be sure to check out the Sandboxie program. David made a nice video about it here: https://wpsecuritylock.com/sandboxie-the-safer-way-to-surf-the-web/
Good luck and stay safe!
I’ve heard that some have conflicts with others, but users can disable one to run the other. Some av programs pick up malware that others don’t.
I have AVG and Malware Bytes running with no conflicts. And I can run Sandboxie too. Plus, I have my router locked down and 2 firewalls. And I make backups of my backups. Hmmm, now I’m showing how OVERLY secure I really am. LOL
My site was infected this morning! I hate GoDaddy. Those people lost a customer. I cleaned it up the same way I cleaned the 3 previous ones. With a Php script that removes that piece of code at the top of every php files. I then reinstalled everything and yet it still comes back.
I am done reloading my GoDaddy hosted sites for clients. 3 years of no probs – then this kicks the S$*@ out of my confidence. 7 calls to them in 10 days, avg lenght of call, 40 mins. Not cool GoDaddy, not cool.
You have had one heck of a bad time. I hope things get better for you soon. I’ve got my fingers crossed your site doesn’t get hit again.
Hey this is nothing when you consider there is a blog in Singapore that was dossed some 37 times in a period of less than one month! No kidding. That is what I heard at least. And it checks out based on all the gaming forums I have visited. So what you’re highlighting here is peanuts when compared to that sort of heavy days. Seems like we are beginning to live in the land of the fee rather than the free even in the US of A.
The problem in Godaddy is not resolved. This Sunday morning i have another hacker intrusion in my godaddy account:
Log of wordpress file monitor:
“This email is to alert you of the following changes to the file system of your website
Timestamp: Sun, 23 May 2010 07:21:51 +0200
Added:
jeremias_scene.php”
No change in my files…
Problem continues….
Get off of GoDaddy. You’ve been through enough.
You guys talk about WordPress but I got hacked on may 20th and I don’t run WordPress but I made a few personal PHP tools using Zend Framework… so if WordPress is running on Zend Framework, I would assume any site running Zend Framework on Go Daddy can be hacked… if not, well, I got hacked anyway 🙂 I simply re-uploaded all of my source and it’s working ok for now.
I’ve had enough.
I left Godaddy for Hostgator and took my 15 WordPress sites with me.
Our site was hack again today (total of 8 times now) The last attack was May 20th like most everyone else. Did anyone else get hit? (hosted on godaddy) Is there anything else I can try? I’ve followed this blog and all of godaddy suggestions, I’ve reinstalled, done all of the security measures and I’m at a total loss. ANY help is appreciated!!
Am in the process of uploading clean files once again.
http://www.sportsthenandnow.com
(infected main site and all subdomains which are running separate WP installs)
Second time today that I am finding new instances of injection on my web-site. Just cleaned everything two days ago… Been exploited 5 or 6 times last month as well. Joomla is up to date, chmod is fine, can’t get my head around this….